A destination target server is stored within the JSON property targets which is an array of JSON objects - each target server is an object within it.
"targets": [{
"sslcontext": {
"excludeprotocols": "SSL,SSLv2,SSLv2Hello,SSLv3",
"allowrenegotiate": false,
"excludeciphersuites": "SSL,SSLv2,SSLv2Hello,SSLv3",
"useciphersuites.order": true,
"includeciphersuites": "TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384,TLS_ECDHE_RSA_,SSL_RSA_WITH_3DES_EDE_CBC_SHA,TLS_RSA_WITH_AES_128_CBC_SHA",
"truststore.type": "JKS",
"truststore.provider": "BC"
},
"scheme": "http",
"port": 8080,
"unavailable": false,
"name": "demoapp1",
"host": "127.0.0.1",
"disabled": false,
"bindaddress": "",
"bindport": 0
"limits": {
"queue.length": 100,
"max.idle.connections.hard": 20,
"idle.ttl": 10,
"max.idle.connections.soft": 5,
"max.concurrent.requests": 20
}
}], |
Within the individual target, sslcontext and limits are optional - if not specified, the relevant settings for the destination itself will be used.
Often, these limits are used to allow more concurrent requests towards one server than toward another in case one have more resources than the other.
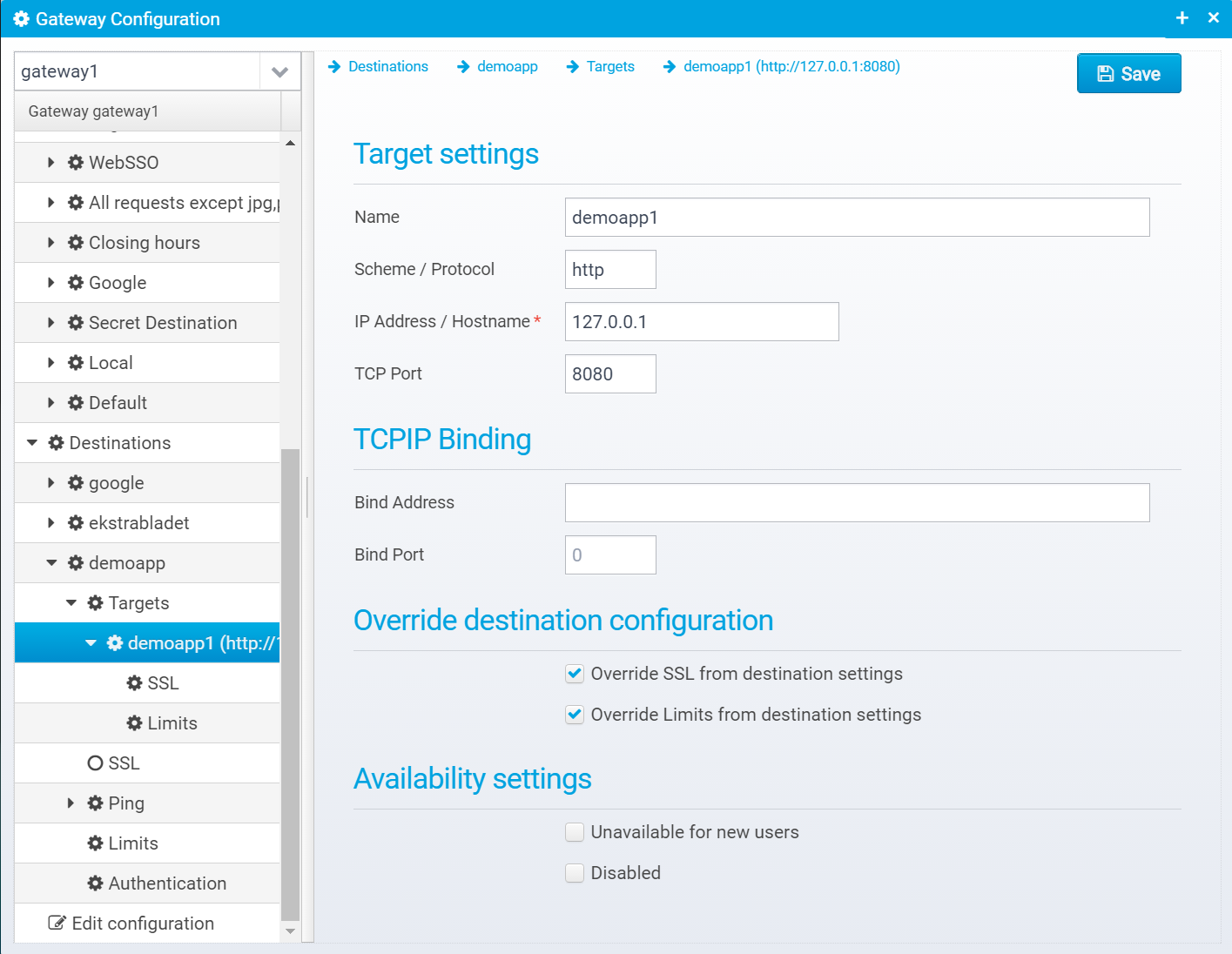
Target name - used to identify the target server selected, and a hash of the name is stored in a cookie, if the server is sticky.
Default: none
JSON key: name
Scheme / Protocol to use when connecting to the server, use http or https
Default: http
JSON key: scheme
IP Address or hostname of server to connect to.
Default: none, must be specified
JSON key: host
TCP Port to connect to, usually 80 for http and 443 for https.
Default: none
JSON key: port
If specified, this is the address to bind to when making the connection to the target server - leave blank to autoassing. This is useful when you want to select a particular network interface.
You can specify either an IP address or a hostname, which will then be resolved to the IP address - this address needs to match a network interface on your machine. |
Default: Uses setting for destination
JSON key: bindaddress
Minimum Version: 5.61
TCP port to bind to when connecting to target server. Set to 0 to autoassign port. Only used when also specifying the bind address
Default: 0
JSON key: bindport
Minimum Version: 5.61
Check to override SSL settings
Default: none
JSON key: If sslcontext JSON Object is present, then override is enabled.
Check to override limits
JSON key: if limits JSON Object is present, then override is enabled.
Check if unavailable for new users - in this case, no new users will be assigned to this destination server.
Default: false
JSON key: unavailable
Check if disabled and no connections should be sent to this target, existing users will failover to other targets
Default: false
JSON key: disabled
If override SSL is enabled, you can specify the SSL settings.
They are saved in the JSON key sslcontext within the targets JSON Object.
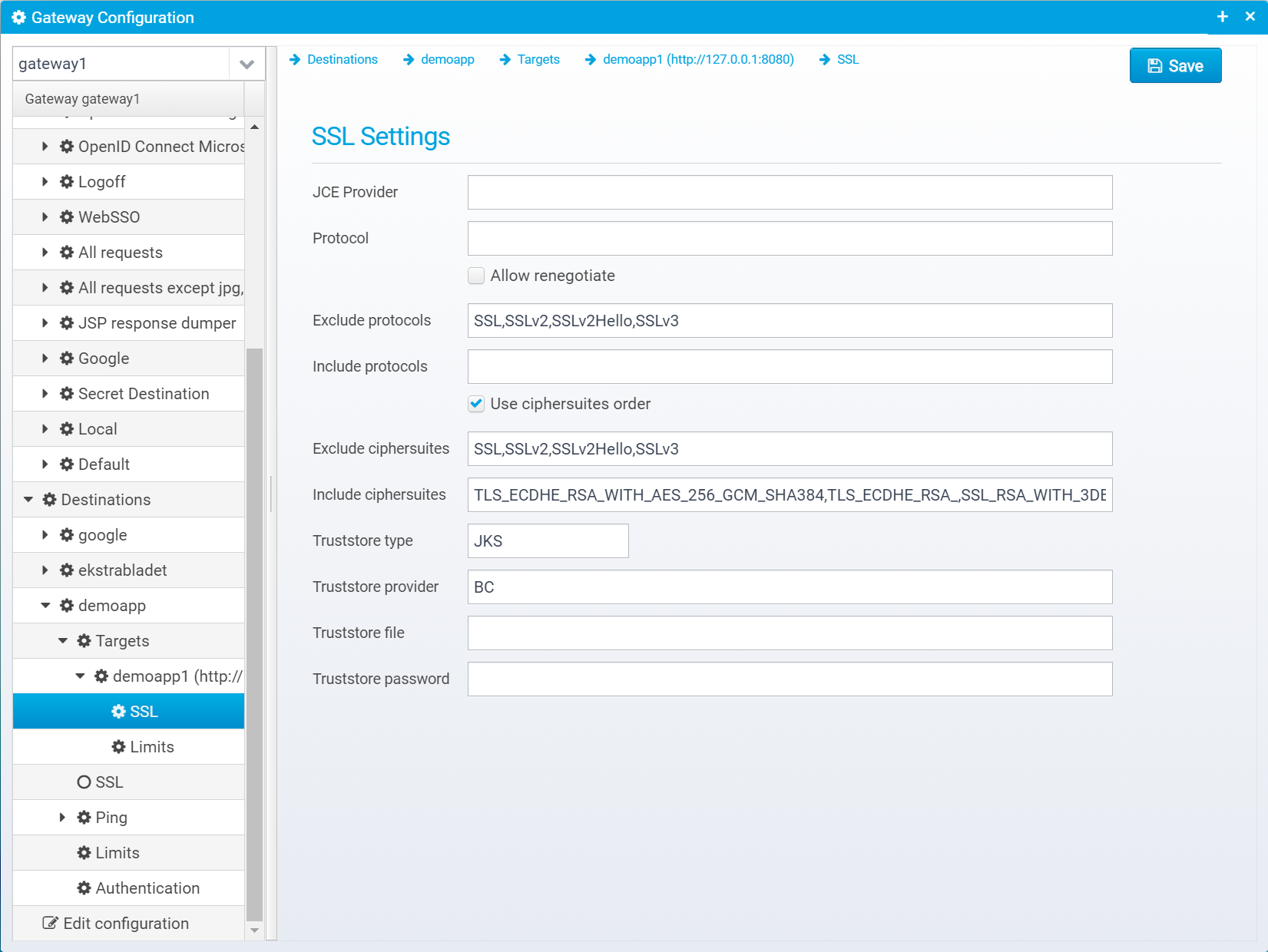
Name of SSL JCE Provider to use, or leave blank for default JDK
Default: blank, meaning JDK default.
JSON key: ssl.provider
Name of SSL Protocol (e.g. TLS), or leave blank for default. Note that some SSL protocols are insecure - but old server implementations might require you to use an older protocol - typical protocols are TLS, TLSv1.1, TLSv1.2
Default: blank, meaning JDK default.
JSON key: ssl.protocol
Allow unsecure renegotiation, turn off for best security.
Default: false
JSON key: allowrenegotiate
Comma/semicolon separated list of SSL protocols to exclude from the JCE default protocols list - patterns are regex expressions.
Default: SSL,SSLv2,SSLv2Hello,SSLv3
JSON key: excludeprotocols
Comma/semicolon separated list of protocols to include from the JCE supported protocols list - patterns are regex expressions
Default: none, meaning JDK default
JSON key:includeprotocols
If set, use configured cipher suites order and prefer first, if not set order does not matter when selecting which cipher suite to use.
Default: true
JSON key: useciphersuites.order
Comma/semicolon separated list of ciphersuites to exclude from the JCE default ciphersuites list - patterns are regex expressions.
Default: .*NULL.*,.*RC4.*,.*MD5.*,.*DSS.*
JSON key: excludeciphersuites
Comma/semicolon separated list of ciphersuites to include from the JCE supported ciphersuites list - patterns are regex expressions
Default: TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384,TLS_ECDHE_RSA_,SSL_RSA_WITH_3DES_EDE_CBC_SHA,TLS_RSA_WITH_AES_128_CBC_SHA
JSON key:includeciphersuites
Type of truststore, e.g. PKCS12, or JKS (default PKCS12
Default: PKCS12
JSON key: truststore.type
Name of JCE provider (default BC)
Default: BC
JSON key: truststore.provider
Name of and path to file containing truststore
Default: none
JSON key: truststore.file
Password for the truststore and keys within - can optionally be encrypted/obfuscated
Default: none
JSON key: truststore.password
If override is enable, the limits can be specified for the specific target server.
Limits are stored in the limits JSON Object inside the specific targets JSON Object.
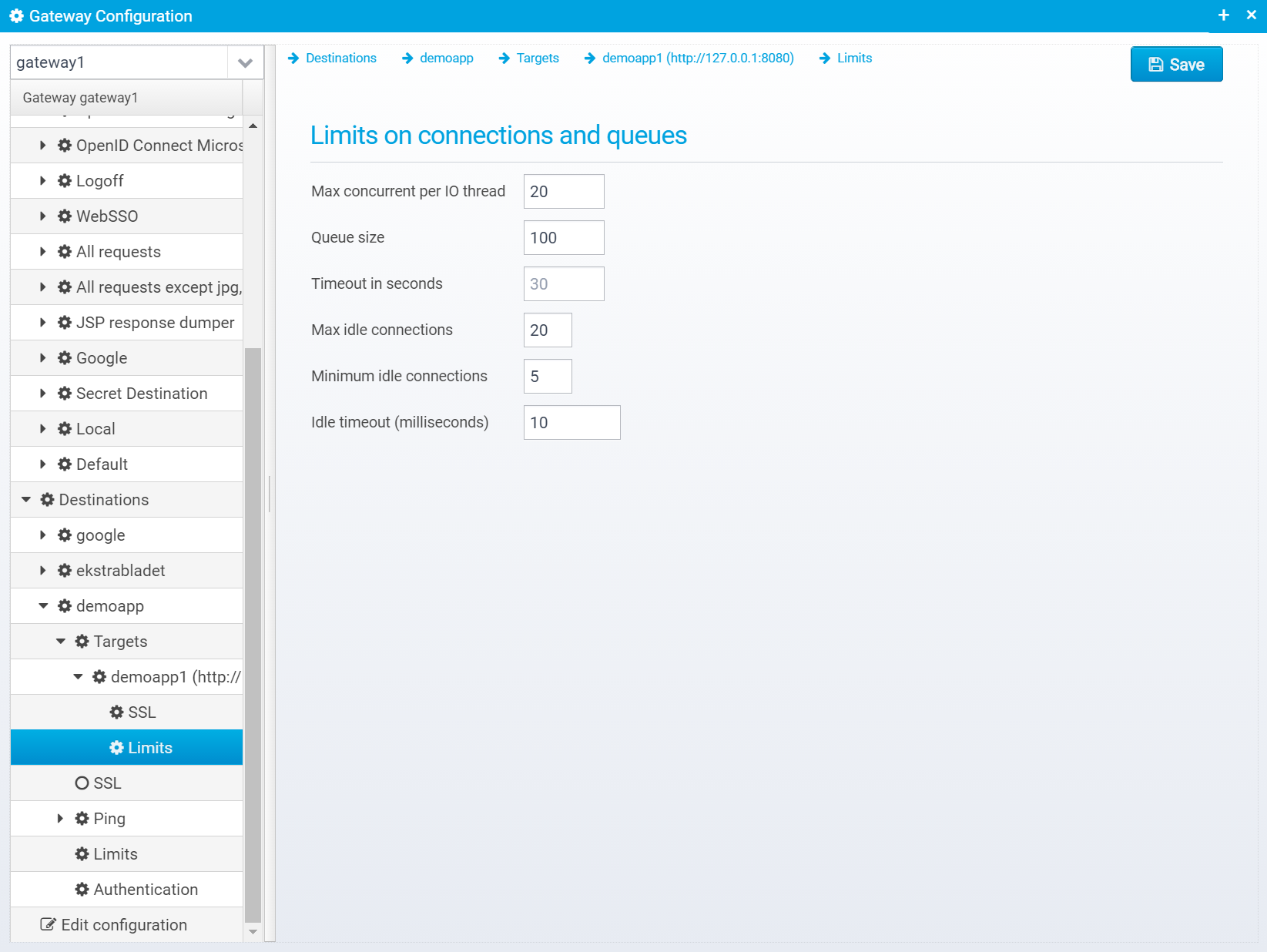
Maximum number of concurrent requests (PER IO THREAD) for a target server, requests above this limit will be queued (default is 20). See the settings for number of IO threads here: Config - Gateway Settings
Default: 20
JSON key: max.concurrent.requests
Number of connections that can be queued waiting for an available connection
Default: 500
JSON key: queue.length
Request timeout in seconds - maximum number of seconds to wait for a reply from the server.
Default: 30
JSON key: timeout.seconds
Maximum number of idle connections to a target server - connections exceeding this count will be closed instead of being pooled for new requests.
Default: 20
JSON key: max.idle.connections.hard
The minimum number of connections that this proxy connection pool will try and keep established. Once the pool is down to this number of connections no more connections will be timed out.
This value is per IO thread, so to get the actual value this must be multiplied by the number of IO threads |
Default: 5
JSON key: max.idle.connections.soft
Number of milliseconds until timing out idle connections above the minimum limit, set to 0 or -1 to disable
Default: -1
JSON key: idle.ttl